Tomcat配置HTTPS实现双向认证
这几天写应用密码学实验写到人傻了……
用到的资源:链接: https://pan.baidu.com/s/1IrFwVIPpc-bAeYQ5R07dxg 提取码: abcd
- 使用openssl生成ca证书并颁发证书的步骤以及运行结果
#ca操作
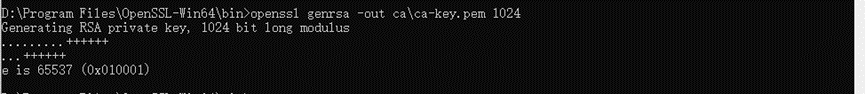
创建ca私钥
openssl genrsa -out ca\ca-key.pem 1024
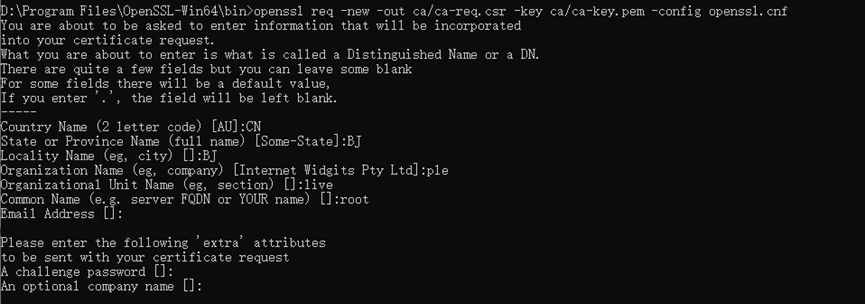
创建证书请求
openssl req -new -out ca/ca-req.csr -key ca/ca-key.pem -config openssl.cnf
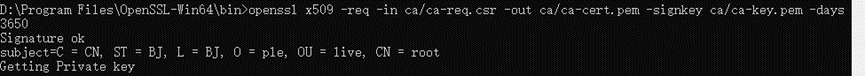
自签署证书
openssl x509 -req -in ca/ca-req.csr -out ca/ca-cert.pem -signkey ca/ca-key.pem -days 3650
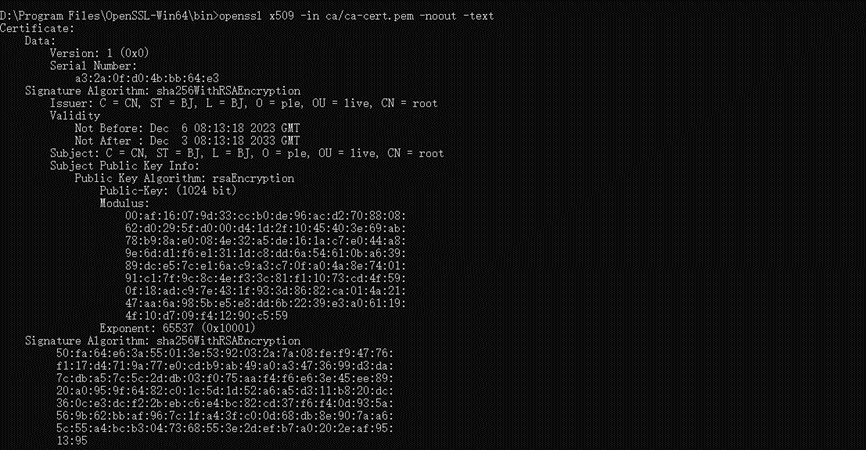
打印证书的内容
openssl x509 -in ca/ca-cert.pem -noout -text
打印证书的序列号
openssl x509 -in ca/ca-cert.pem -noout -serial
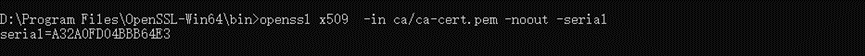
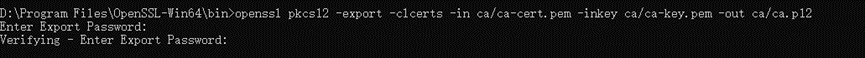
导出证书格式为p12
openssl pkcs12 -export -clcerts -in ca/ca-cert.pem -inkey ca/ca-key.pem -out ca/ca.p12
#下面的为server
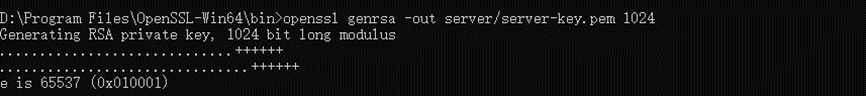
创建server私钥
openssl genrsa -out server/server-key.pem 1024
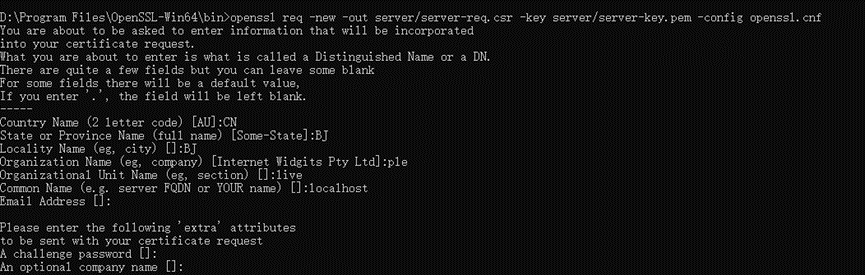
server创建证书请求
openssl req -new -out server/server-req.csr -key server/server-key.pem -config openssl.cnf
CA为server签署证书
openssl x509 -req -in server/server-req.csr -out server/server-cert.pem -signkey server/server-key.pem -CA ca/ca-cert.pem -CAkey ca/ca-key.pem -CAcreateserial -days 3650

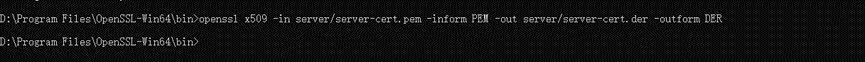
openssl x509 -in server/server-cert.pem -inform PEM -out server/server-cert.der -outform DER
导出证书格式为p12
openssl pkcs12 -export -clcerts -in server/server-cert.pem -inkey server/server-key.pem -out server/server.p12

#下面的为client
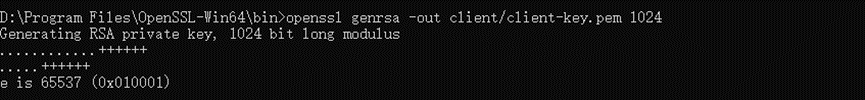
创建server私钥
openssl genrsa -out client/client-key.pem 1024
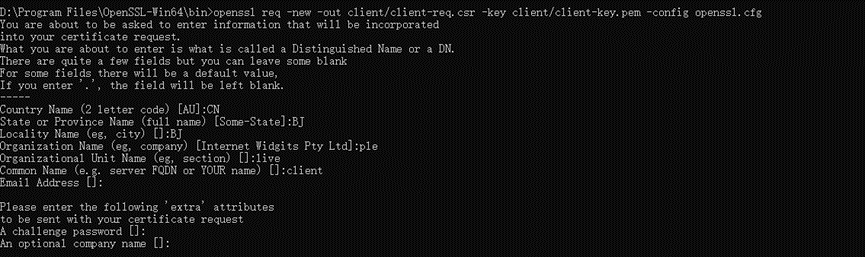
client创建证书请求
openssl req -new -out client/client-req.csr -key client/client-key.pem -config openssl.cfg
CA为client签署证书
openssl x509 -req -in client/client-req.csr -out client/client-cert.pem -signkey client/client-key.pem -CA ca/ca-cert.pem -CAkey ca/ca-key.pem -CAcreateserial -days 3650

导出证书格式为p12
openssl pkcs12 -export -clcerts -in client/client-cert.pem -inkey client/client-key.pem -out client/client.p12
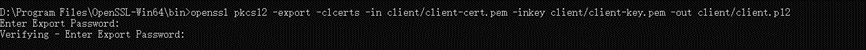
将证书导出成浏览器支持的.p12格式:
openssl pkcs12 -export -clcerts -in client/client-cert.pem -inkey client/client-key.pem -out client/client_err.p12
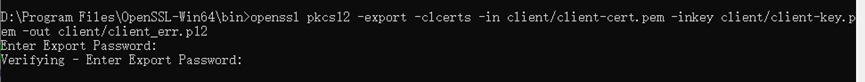
生成客户端证书导出成浏览器支持的.p12格式(用于导入浏览器):
openssl pkcs12 -export -clcerts -in ca/ca-cert.pem -inkey ca/ca-key.pem -out client/client.p12
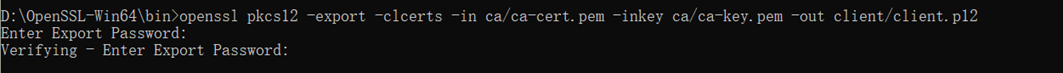
根据ca证书生成jks文件
keytool -keystore D:/OpenSSL-Win64/bin/jks/truststore.jks -keypass 222222 -storepass 222222 -alias ca -import -trustcacerts -file D:/OpenSSL-Win64/bin/ca/ca-cert.pem
- 在网站中使用PKI,配置网站的安全连接https访问的步骤以及效果截图
接下来的内容建议在虚拟机做:
安装tomcat8.0和JavaSE8环境
进入“设置”->“系统”->“关于”->“高级系统设置”->“环境变量”
在“系统变量”中新增变量“JAVA_HOME”,值为JavaSE8安装的地址如“C:\Program Files\Java\jdk1.8.0_331”
编辑Path变量,新增变量“%CATALINA_HOME%\bin”
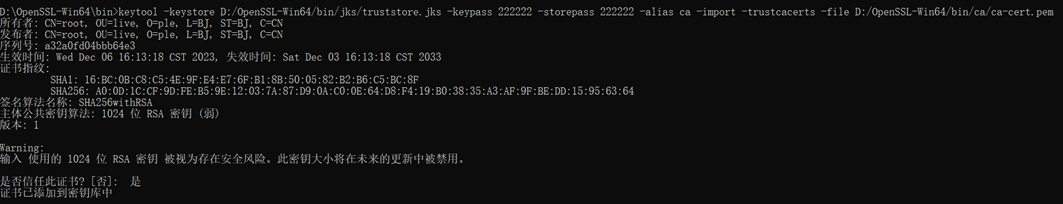
将“server.p12”和“truststore.jks”放在Tomcat的根目录,“server-cert.pem”和“server-key.pem”放在bin目录下
配置cof目录下的“server.xml”,修改为下图所示,“root”为生成“server.p12”时的密码,“222222”为生成“truststore.jks”时的密码
<Connector port="8080" protocol="HTTP/1.1"
connectionTimeout="20000"
redirectPort="443" />
<Connector port="443" protocol="org.apache.coyote.http11.Http11Protocol"
maxThreads="150" SSLEnabled="true" scheme="https" secure="true"
clientAuth="true" sslProtocol="TLS"
keystoreFile="server.p12"
keystorePass="root"
keystoreType="PKCS12"
truststoreFile="truststore.jks"
truststorePass="222222"
truststoreType="JKS"
SSLCertificateFile="../bin/server-cert.pem"
SSLCertificateKeyFile="../bin/server-key.pem"
/>
保存在bin目录下启动“startup.bat”
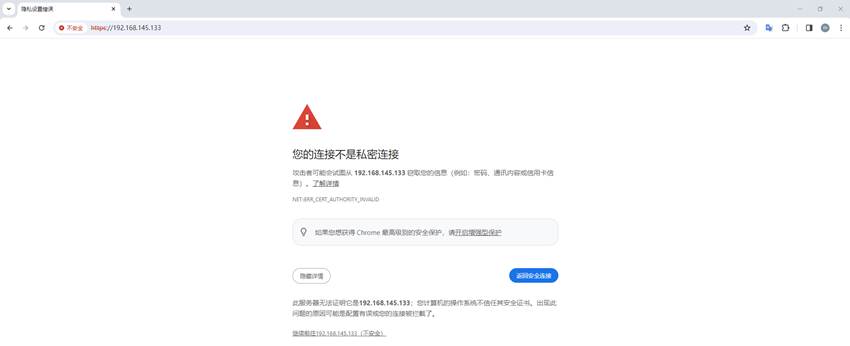
访问https://localhost,https连接显示不安全,这时需要把证书导入到浏览器中
在受信任的跟证书颁发机构导入ca的证书“ca.p12.crt”

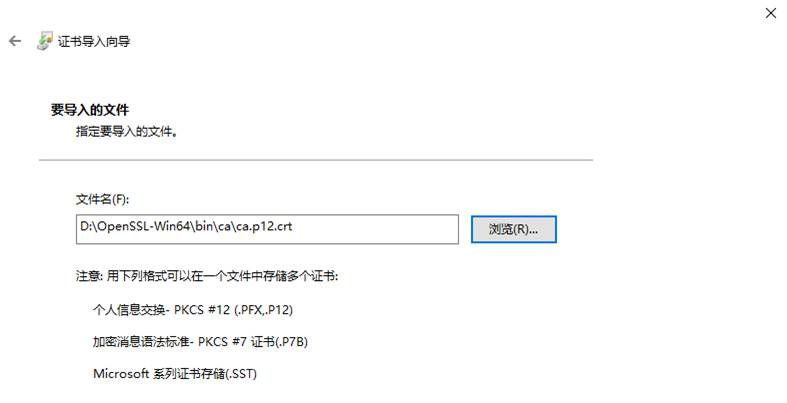
输入生成证书时的密码“root”,一直选择下一步,然后安装证书

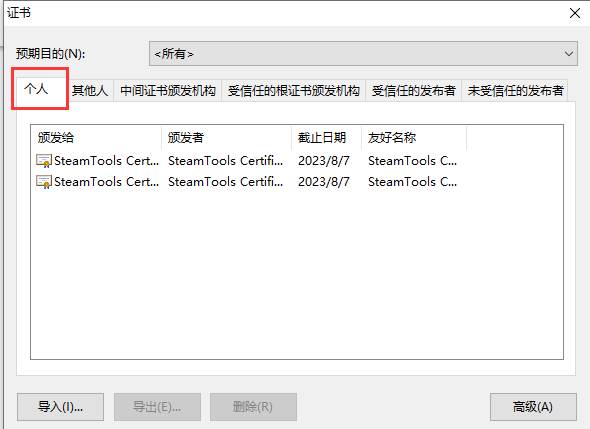
相同步骤,在“个人”中导入client的证书“client.p12.crt”
再次访问https://192.168.145.133/ (localhost的IP),选择证书即可

